As the world’s governments exercise exciting new gag-order snooping warrants that companies can never, ever talk about, companies are trying out a variety of “Ulysses pacts” that automatically disclose secret spying orders, putting them out of business.
A “Ulysses pact” is a negotiating tactic in which one party voluntarily surrenders some freedom of action, named for the story of Ulysses ordering his men to tie him to the mast of his ship so that he couldn’t jump into the sea when he heard the sirens’ song. For example, a union leader heading into a negotiation might promise to resign rather than take a pay cut, making pay-cut demands useless (because if she acceded to such a demand, she’d have to resign before she could formalize the agreement).
In the world of secret spying orders, companies use “warrant canaries” as a kind of dead man’s switch: at regular intervals, they publish a transparency report with statistics for each kind of government request they’ve received, including “Secret spying orders: 0.” After receiving their first secret spying order, they stop publishing that line altogether. If the company sells its service as privacy-oriented, this is, effectively, suicide: the service’s users quit using it, and the spies have nothing.
But it’s a weak kind of Ulysses pact, because a CEO contemplating suicide-by-canary might just decide that one teensy lie isn’t such a big deal after all — and if spy agencies believe that this is the case, they’ll have every reason to use secret warrants, forcing the issue.
But technology gives us a new, stronger kind of Ulysses pact, one that takes the choice out of management’s hands — a self-enforcing self-destruct button, which has the potential to make some secret warrants totally useless: binary transparency.
There’s another kind of secret spying: malware implantation. This is when a government body orders a company to send some of its customers a software update that includes a backdoor. For example, the Saudi government once convinced Research in Motion to backdoor Blackberry devices within its borders. In May, 2014, the anonymously maintained Truecrypt project mysteriously shut down, leaving behind a cryptic note (possibly with a Dan-Brown-esque secret message in it). Many believe that they shut down in response to a government demand to weaken some or all of the Truecrypt programs in the wild.
In the case of programs that run on user’s computers there’s “binary transparency.” When a program with binary transparency receives an update, it computes that update’s “hash” (a mathematical fingerprint) and sends it to a server maintained by a disinterested third party. It also checks the hashes of all the other updates that have been received by all the other versions of the program that have checked in. If it sees that it has got a special update, it refuses to install it and alerts the user.
This is much stronger, more effective Ulysses pact. If a spy agency knows that any attempt to implant malware on a user’s computer through a software update will both fail and raise an alarm, there is absolutely no reason even to try.
‘Warrant canaries’: a subtle hint that your email provider is compromised [The Guardian]
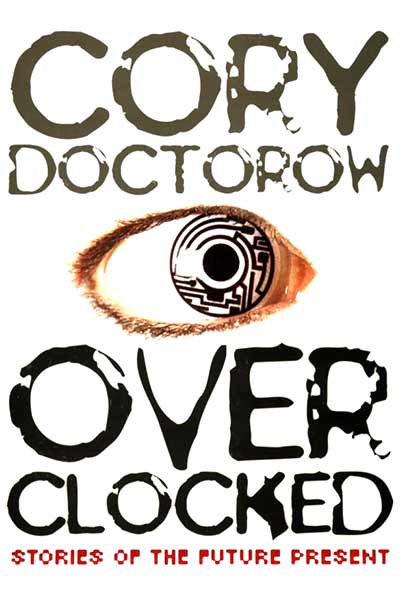
(Image: Herbert James Draper – Ulysses and the Sirens (1910), public domain)